
Executive Summary
The Bottom Line: Email Security Compliance and authentication moved from “best practice” to mandatory requirement in 2025. UK fintech and SaaS companies face regulatory deadlines, compliance penalties up to £100K+, and significant security risks without proper DMARC implementation.
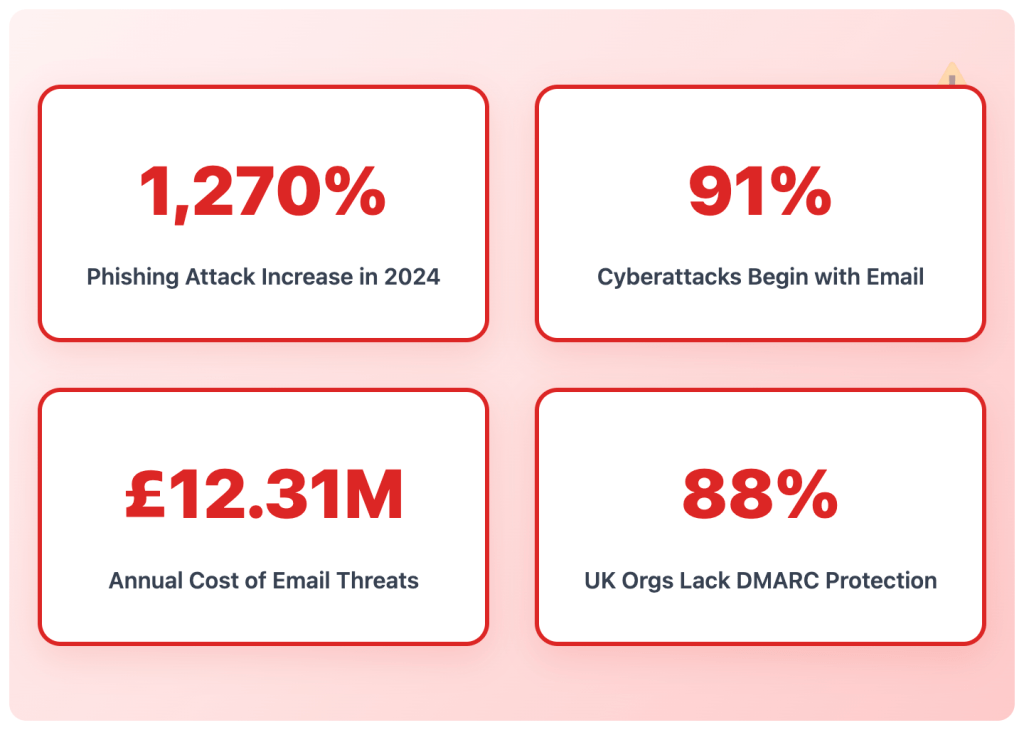
- DMARC compliance mandatory since March 2025 (PCI DSS v4.0)
- Microsoft requires authentication for 5,000+ daily emails (May 2025)
- 91% of cyberattacks begin with email spoofing
- Average incident cost: £4.88 million
- Implementation timeline: 12-16 weeks across 5 phases
Take Action: Get your free email security assessment →
Table of Contents
- Why 2025 Became the Compliance Turning Point
- Understanding Email Authentication (SPF, DKIM, DMARC)
- The Business Case Beyond Compliance
- Implementation Challenges & Solutions
- Industry-Specific Requirements
- Common Mistakes to Avoid
- Strategic Implementation Roadmap
- Ongoing Management Requirements
- Risks of Inaction
- Getting Started with Expert Help
Introduction: The Email Security Turning Point
Please note this blog entry is information presented based on Digistrat’s understanding and research; however does not represent legal advice. We always encourage clients to double-check all of their processes, etc, with their Legal team ultimately.
The email security landscape changed dramatically in 2025. What were once “best practices” have become mandatory requirements, with real consequences for non-compliance. For UK fintech and SaaS companies, this shift represents both a critical challenge and a competitive opportunity.
Since March 2025, DMARC compliance has become mandatory under PCI DSS v4.0 for all organisations processing payment card data, whilst Microsoft now requires DMARC implementation for all senders delivering over 5,000 emails daily to its consumer services. These aren’t optional recommendations; they’re regulatory requirements with significant penalties for non-compliance.
The stakes couldn’t be higher. According to IBM’s latest Data Breach Report, email security threats cost businesses over £12.31 million annually, whilst 91% of cyberattacks begin with phishing emails. For fintech companies handling sensitive financial data and SaaS platforms managing user credentials, email security failures can trigger regulatory investigations, customer churn, and reputational damage that takes years to repair.
🎯 Quick Check: Is Your Company At Risk?
Answer these 3 questions:
- Do you process payment card data? (PCI DSS applies)
- Do you send 5,000+ emails daily? (Provider requirements apply)
- Can criminals easily spoof your domain? (No DMARC = yes)
If you answered “yes” to any question, you need immediate action.
Get Your Free Risk Assessment →
Why 2025 Became the Year of Mandatory Email Authentication

The convergence of three critical factors has made 2025 a watershed moment for email security:
Regulatory Enforcement
PCI DSS 4.0 introduced the requirement that businesses handling payment card data must implement DMARC by March 2025. This affects virtually every UK fintech, from digital banks to payment processors to investment platforms. Non-compliance can result in hefty fines, loss of payment processing privileges, and mandatory security audits.
Provider Requirements
Major email providers have moved beyond recommendations to enforcement. Since February 2024, email providers like Google and Yahoo require stricter email authentication standards, with emails lacking proper SPF, DKIM and DMARC verification being blocked or rejected. Microsoft’s requirements became effective on May 5, 2025, mandating DMARC for all bulk senders.
Escalating Threat Landscape
The Anti-Phishing Working Group (APWG) reports that phishing attacks increased by 1,270% in 2024. Criminal organisations have become more sophisticated, using AI to create convincing spoofed emails that can bypass traditional security measures. Without proper authentication, your domain becomes an easy target for impersonation.
Understanding the Email Authentication Trinity: SPF, DKIM, and DMARC
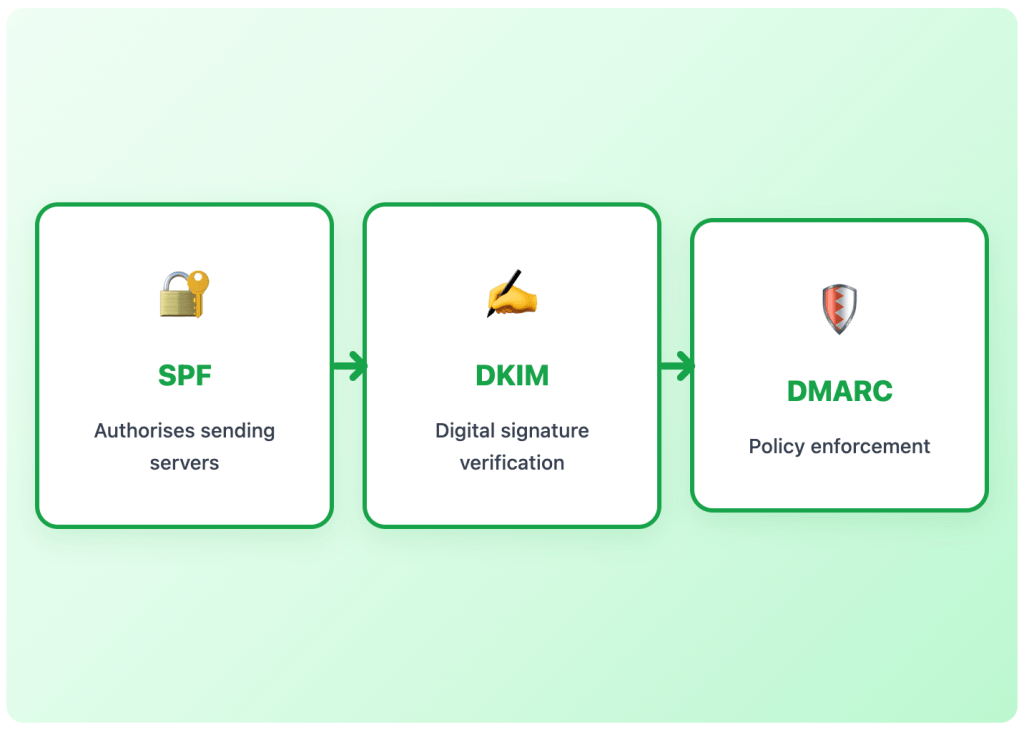
Email authentication relies on three interconnected protocols that work together to verify sender identity and prevent spoofing. Think of them as layers of verification, like showing multiple forms of ID at a bank.
SPF (Sender Policy Framework): The Authorisation List
SPF is a way for a domain to list all the servers they send emails from, like a publicly available employee directory that helps confirm if an employee works for an organisation.
When you publish an SPF record in your DNS, you’re creating a whitelist of IP addresses authorised to send emails from your domain. Mail servers receiving an email can check it against the SPF record before passing it to the recipient’s inbox.
For fintech and SaaS companies, SPF is particularly crucial because you likely send emails from multiple sources: your CRM platform, customer support system, billing software, and marketing tools. Each needs explicit authorisation.
DKIM (DomainKeys Identified Mail): The Digital Signature
DKIM adds a digital signature to your email header, proving that the message hasn’t been altered in transit and confirming the email came from an authorised domain.
The process works through cryptographic key pairs: your private key is kept secret by the sender, who signs the email’s header with this key, whilst mail servers receiving the email can verify that the sender’s private key was used by applying the public key.
This is essential for transactional emails like password resets, payment confirmations, and security alerts, the types of messages that criminals most commonly attempt to forge.
DMARC: The Policy Enforcement Layer
DMARC tells a receiving email server what to do given the results after checking SPF and DKIM. A domain’s DMARC policy can instruct mail servers to quarantine emails that fail SPF or DKIM (or both), to reject such emails, or to deliver them.
DMARC provides three policy levels:
- p=none: Monitor only (no enforcement action)
- p=quarantine: Send failing emails to spam folder
- p=reject: Block failing emails entirely
DMARC also provides detailed reporting about the successes and failures of handling emails claiming to be from your domain, helping you identify unauthorised use.
⏱️ Implementation Reality Check
Typical Timeline for Full DMARC Enforcement:
- Small company (1-2 domains): 8-12 weeks
- Mid-market (multiple domains/services): 12-16 weeks
- Enterprise (complex infrastructure): 16-24 weeks
Don’t wait – March 2025 PCI DSS deadline has passed. Start now.
The Business Case: Beyond Compliance

Whilst regulatory requirements might be driving initial implementation, the business benefits of proper email authentication extend far beyond compliance.
Deliverability Improvements
Current inbox placement rates average around 85%, with significant variations across providers. Proper authentication can dramatically improve these rates. Authenticated domains are trusted by email providers, leading to better inbox placement and higher engagement rates.
Brand Protection
Without DMARC, criminals can easily spoof your domain to send phishing emails to your customers. Attackers can impersonate a company’s email address to deceive customers or employees, potentially resulting in data breaches or financial fraud. This doesn’t just create security risks; it damages customer trust and brand reputation.
Operational Efficiency
Failed authentication leads to increased customer support tickets as users don’t receive critical emails. Password reset emails in spam folders, missing transaction confirmations, and blocked security alerts all generate support burden and customer frustration.
Competitive Advantage
Companies that implement comprehensive email authentication early gain several advantages: improved customer communication reliability, reduced security incident response costs, and the ability to move faster with email-based features knowing their infrastructure is secure.
Implementation Challenges: Why Many Companies Struggle
Despite clear requirements and obvious benefits, many organisations struggle with email authentication implementation. Understanding these challenges helps explain why expert guidance is often necessary.
Technical Complexity
Depending on the complexity of your environment, implementation could be significant. If you are not a DMARC expert, it can take a lot of time to work out the kinks related to blocking the right emails and letting valid emails through.
Modern organisations often have complex email ecosystems with multiple sending sources, third-party integrations, and legacy systems. Each needs proper configuration to avoid breaking legitimate email flow.
Phased Approach Requirements
Microsoft recommends a gradual approach to setting up DMARC, starting with a DMARC policy of p=none and monitoring the results for the domain. This phased implementation prevents legitimate emails from being blocked but requires ongoing monitoring and adjustment.
Resource Constraints
Many IT teams are already stretched thin with other priorities. Email authentication requires dedicated attention, ongoing monitoring, and expertise that many organisations lack internally.
Risk of Email Disruption
It is critical to understand the impact of setting a DMARC policy as it could have significant implications on email delivery. Incorrect implementation can block legitimate emails, disrupting business operations and customer communications.
Industry-Specific Considerations for UK Fintech and SaaS

Different business models face unique email authentication challenges that require tailored approaches.
Fintech-Specific Requirements
UK fintech companies face particularly stringent requirements due to their regulatory environment:
PCI DSS Compliance: Any business that processes, stores, or transmits payment card information is subject to PCI DSS requirements, and the DMARC mandate is no exception. This includes retailers, financial institutions, payment processors, and service providers.
High-Risk Communications: Fintech companies regularly send high-value transactional emails containing sensitive financial information. Payment confirmations, e-invoices, 2FA codes, and new device logins must be delivered instantly with no hiccups whatsoever.
Regulatory Oversight: Financial services regulators increasingly view email security as part of operational resilience requirements. Authentication failures can trigger regulatory questions and mandatory security reviews.
SaaS Platform Challenges
SaaS companies face different but equally significant challenges:
User Onboarding Dependencies: Trial users churn without activation when onboarding sequences fail to reach inboxes. Email deliverability directly impacts conversion rates and user activation metrics.
Multi-Tenant Complexity: Many SaaS platforms send emails on behalf of their customers, requiring careful subdomain management and authentication to maintain reputation across all sending domains.
Scale Requirements: High-growth SaaS companies can quickly exceed the 5,000 daily email threshold that triggers mandatory authentication requirements across all major providers.
💡 Pro Tip: Start with High-Risk Communications
Prioritise authentication for:
- Password reset emails
- Payment confirmations
- 2FA codes
- Security alerts
- Onboarding sequences
These failures cause immediate business impact.
Common Implementation Mistakes and How to Avoid Them
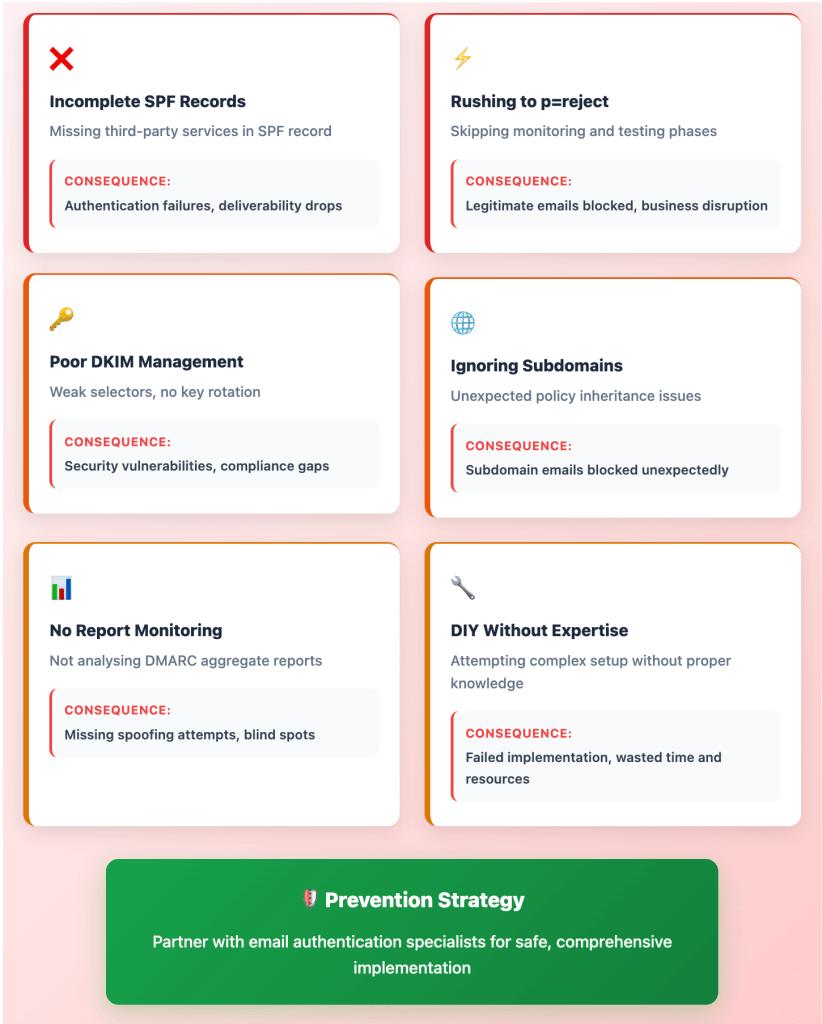
Even with clear requirements, many organisations make costly mistakes during email authentication implementation. Here are the most common pitfalls:
Incomplete SPF Records
Many companies list their primary sending servers but forget about third-party services like CRM platforms, customer support tools, or marketing automation systems. Each mechanism must be explicitly listed to avoid logical conflicts in your SPF record.
DKIM Selector Management
It’s recommended to use descriptive selectors and rotate keys regularly (for example, yearly). Poor selector naming and infrequent key rotation can create security vulnerabilities and operational confusion.
Rushing to Enforcement
Moving too quickly from monitoring (p=none) to enforcement (p=reject) without sufficient testing can block legitimate emails. Each subdomain requires careful testing and verification along the way to prevent destination email systems from rejecting good mail.
Ignoring Subdomain Management
Unlike SPF and DKIM, the DMARC TXT record for a domain automatically covers all subdomains that don’t have their own DMARC TXT record. This can create unexpected policy inheritance that blocks legitimate emails from subdomains.
Inadequate Monitoring
DMARC provides detailed reports about authentication attempts, but many organisations lack the expertise to properly analyse and act on this data. Without proper monitoring, authentication failures go unnoticed until they cause operational problems.
The Strategic Implementation Roadmap

Successful email authentication requires a structured approach that balances security requirements with operational continuity. Here’s the proven roadmap:
Phase 1: Assessment and Planning (Weeks 1-2)
- Inventory all email sources: Document every system that sends emails from your domains
- Review current authentication: Check existing SPF, DKIM, and DMARC records
- Assess compliance gaps: Identify specific requirements for your industry and sending volume
- Plan subdomain strategy: Decide how to structure authentication across all domains and subdomains
Phase 2: Foundation Setup (Weeks 3-4)
- Implement SPF records: List all authorised sending sources
- Configure DKIM signing: Set up cryptographic signatures for all sending systems
- Deploy DMARC monitoring: Start with p=none policy to gather intelligence
- Establish reporting analysis: Set up systems to receive and analyse DMARC reports
Phase 3: Testing and Optimisation (Weeks 5-8)
- Monitor authentication results: Analyse DMARC reports to identify issues
- Fix authentication failures: Address any legitimate emails failing checks
- Test subdomain inheritance: Verify policies work correctly across all subdomains
- Validate third-party services: Ensure all external sending sources are properly authenticated
Phase 4: Gradual Enforcement (Weeks 9-12)
- Move to quarantine policy: Implement p=quarantine to catch remaining issues
- Monitor for false positives: Watch for legitimate emails being quarantined
- Address final authentication gaps: Fix any remaining configuration issues
- Prepare for full enforcement: Plan transition to p=reject policy
Phase 5: Full Enforcement and Monitoring (Week 13+)
- Implement reject policy: Move to p=reject for complete protection
- Establish ongoing monitoring: Set up alerts for authentication failures
- Regular security reviews: Quarterly assessments of authentication health
- Incident response procedures: Processes for handling authentication emergencies
🔄 Implementation Success Factors
What separates successful implementations:
✅ Phased approach – Don’t rush to p=reject
✅ Comprehensive testing – Monitor for 4+ weeks per phase
✅ Stakeholder alignment – IT + Marketing + Compliance working together
✅ Expert guidance – Complex implementations benefit from specialised help
✅ Ongoing monitoring – Authentication requires continuous management
FYI – Most failures happen because companies skip the testing phases.
Ongoing Management: Making Authentication Sustainable
Email authentication isn’t a “set and forget” technology. It requires ongoing management to maintain effectiveness and adapt to changing business needs.
Regular Monitoring Requirements
DMARC reports give administrators the information they need to decide how to adjust their DMARC policies and monitor for unauthorised use of domains. This requires dedicated resources to analyse reports, investigate authentication failures, and respond to potential security incidents.
Infrastructure Changes
As your business grows and changes, your email authentication needs will evolve. New third-party services, domain acquisitions, and system migrations all require authentication updates. Without proper change management, authentication can break during routine infrastructure changes.
Threat Evolution
Criminal techniques constantly evolve, requiring ongoing adjustments to authentication policies. What works today may not provide adequate protection tomorrow, making regular security reviews essential.
Compliance Monitoring
Regulatory requirements continue to evolve, with new mandates and updated standards appearing regularly. Staying compliant requires ongoing attention to regulatory changes and proactive policy updates
The Cost of Inaction: Risks of Poor Email Security
For organisations still hesitating about email authentication implementation, understanding the risks of inaction can help clarify the urgency.
Regulatory Penalties
Companies that fail to comply with PCI DSS 4.0 DMARC requirements could face severe penalties during PCI audits, including hefty fines, reputational damage, and even loss of payment processing privileges.
Security Incident Costs
The average cost per spoofed email incident is £4.88 million. A single successful domain spoofing attack can trigger customer data breaches, regulatory investigations, and massive remediation costs.
Operational Disruption
Without proper authentication, legitimate emails increasingly fail to reach recipients. This creates customer support burdens, reduces marketing effectiveness, and can disrupt critical business processes dependent on email communication.
Competitive Disadvantage
Companies with poor email deliverability struggle to compete effectively. When your marketing emails land in spam folders and your transactional emails get blocked, customer engagement suffers and business growth slows.
Brand Reputation Damage
In worst-case scenarios, continued non-compliance could cause businesses to lose customer trust, resulting in loss of business and credibility.

Choosing the Right Implementation Partner
Given the complexity and stakes involved, many organisations benefit from expert guidance during email authentication implementation. Here’s what to look for in an implementation partner:
Technical Expertise
Look for partners with deep understanding of email authentication protocols, experience with complex enterprise implementations, and proven track records of successful DMARC deployments to enforcement level.
Industry Knowledge
Choose partners who understand your specific industry requirements, regulatory environment, and business model. Generic email consultants may not appreciate the unique challenges facing fintech or SaaS companies.
Ongoing Support
Email authentication requires ongoing management, not just one-time setup. Ensure your partner can provide continuous monitoring, regular security reviews, and incident response support.
Implementation Methodology
The best partners use structured, phased approaches that minimise risk while ensuring comprehensive protection. Avoid anyone promising overnight solutions or guaranteeing zero implementation risks.
Future-Proofing Your Email Security Strategy
Email authentication requirements will continue to evolve, making future-proofing an essential part of your strategy.
Emerging Technologies
Technologies like BIMI (Brand Indicators for Message Identification) are gaining adoption, allowing companies with DMARC to display logos next to emails in recipients’ inboxes, enhancing brand recognition, trust, and email deliverability.
Increasing Automation
AI and machine learning increasingly influence email filtering decisions. Email providers are using AI to detect and filter out low-quality, mass-sent, or irrelevant content, with systems continuously analysing multiple emails and behavioural signals.
Stricter Requirements
Engagement-based filtering means recipient engagement metrics such as open rates, click-throughs, and replies now determine email deliverability. Future requirements will likely become even more stringent.
Global Harmonisation
As email authentication becomes mandatory across different jurisdictions, international standards are likely to converge, potentially requiring additional compliance measures for companies operating globally.
Conclusion: The Time for Action Is Now
Email authentication has moved from best practice to business imperative. With regulatory deadlines already passed and enforcement underway, the question isn’t whether to implement comprehensive email security—it’s how quickly you can achieve full compliance whilst maintaining operational continuity.
The organisations that thrive will be those that treat email authentication as strategic infrastructure rather than technical overhead. They’ll achieve faster customer communication, improved security posture, and competitive advantages that compound over time.
For UK fintech and SaaS companies, the choice is clear: implement comprehensive email authentication now, or face escalating risks that threaten both compliance and competitive positions.
Take Action: Secure Your Email Infrastructure Today
Don’t let email security vulnerabilities threaten your business. Digistrat specialises in helping UK fintech and SaaS companies achieve comprehensive email authentication whilst maintaining operational excellence.
Get Your Free Email Security Assessment
Discover exactly where your email infrastructure stands against 2025 compliance requirements. Our comprehensive assessment reveals:
- Authentication gaps that expose your domain to spoofing
- Deliverability issues reducing your email effectiveness
- Compliance risks that could trigger regulatory penalties
- Quick wins for immediate security improvements
Book Your Free Assessment Call →
Ready for Complete Email Security?
Our Email Deliverability & Strategy Audit provides everything you need to get you on the road to achieve full DMARC compliance:
- Complete email infrastructure security blueprint
- Sender reputation and risk analysis
- Strategic roadmap with prioritised action plan
- 90-minute executive walkthrough plus implementation support
Start Your Email Deliverability Audit →
Ongoing Protection and Management
For businesses requiring continuous email security management, our Ongoing Email Deliverability & DMARC Monitoring service provides:
- Proactive DMARC monitoring and advancement to p=reject
- Continuous reputation management and threat response
- On-demand expert counsel for campaigns and technical issues
- Monthly strategy reviews and comprehensive reporting
About Digistrat: We’re the UK’s specialist email deliverability consultancy for fintech, SaaS, and consumer app companies. Our expertise ensures your critical emails reach customers’ inboxes whilst protecting your domain from fraud and spoofing attacks.
